 This article makes the case for routine, scalable preservation of potentially-relevant iPhone and iPad data by requiring custodians back up their devices using iTunes (a free Apple program that runs on PCs and Macs), then compress the backup for in situ preservation or collection.
This article makes the case for routine, scalable preservation of potentially-relevant iPhone and iPad data by requiring custodians back up their devices using iTunes (a free Apple program that runs on PCs and Macs), then compress the backup for in situ preservation or collection.
The Need
Most of you will read this on your cell phone. If not, it’s a virtual certainty that your cell phone is nearby. Few of us separate from our mobile devices for more than minutes a day. On average, cell users spend four hours a day looking at that little screen. On average. If your usage is much less, someone else’s is much more.
It took 30 years for e-mail to displace paper as our primary target in discovery. It’s taken barely 10 for mobile data, especially texts, to unseat e-mail as the Holy Grail of probative electronic evidence. Mobile is where evidence lives now; yet in most cases, mobile data remains “off the table” in discovery. It’s infrequently preserved, searched or produced.
No one can say that mobile data isn’t likely to be relevant, unique and material. Today, the most candid communications aren’t e-mail, they’re text messages. Mobile devices are our principal conduit to online information, eclipsing use of laptops and desktops. Texts and app data reside primarily and exclusively on mobile devices.
No one can say that mobile data isn’t reasonably accessible. We use phones continuously, for everything from games to gossip to geolocation. Texts are durable (the default setting on an iPhone is to keep texts “Forever”). Mobile content easily replicates as data backed up and synched to laptops, desktops and online repositories like iCloud. The mobile preservation burden pales compared to that we take for granted in the preservation of potentially-relevant ESI on servers and personal computers.
Modest Burden. That’s what this article is about. My goal is to demonstrate that the preservation burden is minimal when it comes to preserving the most common and relevant mobile data. I’ll go so far as to say that the burden of preserving mobile device content, even at an enterprise scale, is less than that of preserving a comparable volume of data on laptop or desktop computers. Too, the workflows are as defensible and auditable as any we accept as reasonable in meeting other ESI preservation duties.
Three Principles
The following three principles underscore the need for efficient, defensible preservation of relevant mobile content:
- When mobile data may be unique and relevant, it should be preserved in anticipation of litigation. This principle is especially compelling when the preservation burden is trivial (as by use of the backup technique described below). You can demonstrate the absence of relevant data by, e.g., sampling the contents of devices; but standing alone, a policy barring the use of a device to store relevant data is not sufficient proof that such device has not, in fact, been used to store data. Too often, practice belies policy, particularly for messaging
- Mobile preservation should be a customary feature of a defensible litigation hold; but absent issues of spoliation, few matters warrant the added cost of mobile preservation by forensics experts or the burden and disruption of separating users from mobile devices.
- Legitimate concerns respecting personal privacy and privilege do not justify a failure to preserve relevant mobile data, although they will dictate how data is protected, processed, searched, reviewed and produced.
Three Provisos:
As you look at the exemplar workflow ponder how you might adapt it to your needs, consider the following three provisos:
- The method discussed is but one simple, scalable and defensible method to preserve iPhone content. It’s not necessarily the only way or the optimum way.
- Preservation isn’t production. Lawyers’ abilities to search, review and produce mobile content in utile and complete forms hasn’t kept pace with the obligation to do so, or on a par with other responsive sources of ESI. This article is about routine preservation; it doesn’t address downstream processes and production except insofar as ensuring that the information preserved remains readily amenable to all methods of search, review and production in e-discovery.
- Please challenge, but don’t dismiss. The duty to preserve is real and immediate; but there’s room for honest debate about what depth and exactitude of mobile preservation is warranted case to case. In weighing any method, compare it to the alternative. If you reject a preservation method because you deem it flawed, is the alternative a superior method or nothing at all? “None” is rarely the proper choice when it comes to mobile evidence. Preserving “most” is better than “none,” but, considerations of risk may dictate that one preserve “all” over “most.” In turn, considerations of proportionality may elevate “most” over “all.” It’s sensible to ask, “Is the incremental cost of forensic-level preservation by experts justified by relevant and unique content? If not, might ‘good’ be good enough?”
Defensibility
Ignoring mobile evidence isn’t the path taken by competent, ethical attorneys. We must employ methods of preservation that aren’t unduly costly or burdensome yet pose little risk that a judge will find the methods unreasonable. The essence of defensibility is the ability to show that an action was prudent per a good faith assessment of what was known, or in the exercise of diligence should have been known, when the action occurred. If mobile content required to be preserved is lost, the Court will ask: “Was the preservation method employed reasonably calculated to guard against loss or corruption of potentially-relevant mobile data?” This will entail consideration of the method, its deployment and its oversight. These considerations are addressed below in Audit and Verification.
Custodian-Directed Preservation
The predominant approach to preservation in e-discovery entails use of a legal hold directive instructing custodians to act to preserve potentially-relevant ESI. This is custodian-directed preservation, and it’s been justifiably criticized for its many flaws, among them that:
- It requires custodians to make judgments concerning relevance, materiality and privilege;
- It obliges custodians to complete tasks, like lexical search, without proper tools or training;
- It demands effort without affording custodians the time, resources and guidance to succeed; and
- It doesn’t deter custodians who seek to destroy or change inculpatory or embarassing data.
Custodian-directed preservation is key to a defensible legal hold process; however, it’s just part of a proper process and is best paired with other efforts, like IT-initiated holds, that defray its shortcomings.
So, if custodian-directed preservation is problematic, why put custodians in charge of preserving their own devices instead of handing the devices over to digital forensics experts for imaging? Isn’t that inviting the fox to guard the hen house?
The signal challenge to preserving mobile devices is persuading custodians to part with them. By empowering custodians to preserve the data themselves, custodians need never surrender custody of their devices. Accordingly, users are less threatened by the process and less inclined to fight or subvert it. Backing up an iPhone is simple and quick; and crucially, the process affords the custodian neither the need nor the practical ability to select or omit content. Compare that to tasking a custodian to collect e-mail or documents, where it’s easy to overlook or deliberately omit material with little chance of detection.
The advantages of custodian-directed preservation of mobile devices by backup are:
- Custodians keep their phones;
- Custodians need not make judgments concerning relevance, materiality and privilege;
- Custodians need not run searches or possess special tools or skills;
- The backup process is speedy and easy to administrate and autheticate;
- Backups are hard to alter, and it’s difficult to omit content from a backup.
Scalability and Proportionality
Scalability describes the ability of a system or process to handle a growing number of tasks or a larger volume of data. It’s a crucial consideration in all phases of e-discovery, but particularly challenging when dealing with mobile data. Historically, preserving mobile data was a one-off task: seldom undertaken and typically for only a handful of devices. Preserving the contents of a single phone by engaging a digital forensics specialist to image the device was the norm, and though costly, the obligation rarely had to scale to dozens or hundreds of far-flung devices. For one or two phones, you could do it in a day or two for, say, a thousand dollars.
Now, imagine you must preserve the texts and call data from the mobile devices of sales reps, one each in all fifty United States, the District of Columbia, Puerto Rico and Guam. Fifty-three iPhones. What are your options? Let’s compare:
[My cost projections are educated guesses and—please–not an invitation for enterprising readers to post comments extolling their company’s superior pricing.]
- Instruct all custodians to overnight courier their phones to your trusty forensic examiner. In turn, the examiner will image each device and overnight each back when the work is complete.
- Cost: Under $30,000.00 without rush or overtime fees.
- Timing: Assuming no glitches, most users will have their phones back within about four to five business days, as few labs possess the equipment permitting them to image more than a couple of phones simultaneously. As well, 53 packages must be correctly processed, logged as evidence, re-packaged and returned to the correct custodian.
- How many businesses can idle their national sales staff for four to five days?
- How many reps will be willing to hand over their phones for four to five days?
- Send your trusty forensic examiner to 53 locations to image each phone.
- Cost: $50-$60,000.00 in professional time; add a comparable sum for travel costs.
- Timing: A month or more. It’s a 19-hour flight to Guam, 11 hours to Hawaii and nine to Alaska. Equipment must travel, and each custodian must part with their phone for the better part of a day.
- Caveat: Some states license forensic examiners. It may not be legal for an unlicensed examiner to come into the jurisdiction to acquire the image.
- Engage 53 local, licensed (as required) examiners to image each device.
- Cost: $35-$50,000.00 in examiner fees, plus the professional time required to locate, vet and contract with each examiner. There will also be travel time assessed, albeit with little airfare and hotel expense.
- Timing: Weeks, at best. Fifty-three data sets from as many senders must be correctly packaged and returned to you, and each custodian must still part with their phone.
All three options implicate proportionality concerns. All are expensive, disruptive and time-consuming. Accordingly, many litigants opt not to preserve the content of mobile devices, claiming phones don’t hold relevant data in the face of compelling contrary evidence and a dearth of supportive metrics.
Let’s compare the custodian-directed option:
- Direct and instruct 53 custodians to back up their devices, collecting the data as desired.
- Cost: None, insofar as discrete expenditures. Of course, discovery is never “free” because time costs money. The expense to notify the custodians and follow up on compliance is attendant to all methods, and administrative costs don’t count against any. Expenses, if any, for the custodian-directed method hinge on whether you preserve backup data in situ, collect it via network transfer or ship it on physical media. Each method demands some effort of each custodian, whether that entails coordinating with an examiner to tender and retrieve a device or connecting the device to a computer for an iTunes backup. The latter is far easier and least disruptive.
- Timing: A day or two. Sure, some custodians may be on vacation, and some may miss or ignore the request; however, such risks afflict every method. Only the custodian-directed method makes it possible to preserve the many, widespread devices in hours, not days or weeks. The custodian need only get to a computer with the device, whereas a forensic examiner must get to the device or the device must get to the examiner.
The custodian-directed method scales easily for phones and tablets. Custodians need never part with their devices, so there is no business interruption. It’s speedy. It requires no special tools, cabling or software and no technical expertise. Moreover, the process poses almost no risk of loss or alteration of the relevant data and is unlikely to prompt custodians to game the process. There are no operating system compatibility issues. Remote screen-sharing handily facilitates any desired oversight and audit. In short, cost and burden are so trivial that relevance alone should be the pole star in deciding whether to preserve mobile content.
For an example of mobile backup instructions that might be directed to a custodian, look at the appendix to this article or download it here.
Audit and Verification
Recently, my friend and fellow forensic examiner, Scott Moulton, visited New Orleans. Over beignets and café au lait in the French Quarter, I made the case for the preservation methodology described here. Scott’s a brilliant examiner and hard-eyed skeptic. I wanted him to kick the tires and find flaws.
At first, Scott wouldn’t take off his forensic examiner hat and don an e-discovery thinking cap. He extolled the benefits of hiring a qualified forensic examiner and the specialized forensics tools we use to dig for esoteric artifacts. “Hire me. Hire you!” I liked the sound of that, and Scott liked the idea of motorcycling through the lower 48 and D.C. gathering digital evidence like some two-wheeled remake of Cannonball Run meets Revenge of the Nerds.
Still, Scott conceded that in the context of e-discovery, there really isn’t much iPhone data preserved using a costly forensics tool versus preservation using iTunes. Our training and tool sets don’t add much when preserving mobile data for discovery.
Once Scott warmed to the methodology for its speed and low cost, he questioned how the process could be quality checked for integrity. “What if the backup was interrupted or failed,” he asked, “How would we know?”
It’s a good point. Most experienced forensic examiners have found an image acquired in the field to be incomplete or unusable back in the lab. Thankfully, it’s rare; but, sooner or later, it happens. There are always gremlins. Custodial-initiated preservation benefits from oversight and audit, if only because the risk of gremlins feels greater when custodians are in charge.
If iTunes successfully completes a backup, the backup event can be verified several ways:
- In iTunes (with the device connected), by looking at the device summary for the attached device and noting the latest backups. See Fig. below.

- In iTunes (with or without the device connected), under Edit>Preferences>Devices. This lists the backed-up devices by name with time of backup. Hovering the mouse pointer over a listing will bring up further details about the device backed up (model, software version and build, serial number, phone number, IMEI and MEID). See Fig. below.

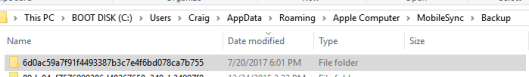
- By confirming the date and time values for the folder containing the latest backup (stored by default in: C:\Users\user’s account name\AppData\Roaming\Apple Computer\MobileSync\Backup\). See Fig. below.
There are several sensible ways to verify and audit a custodian-directed preservation effort. Tailor the method you use to the potential for failure and the willingness of a sponsoring witness to vouch for the integrity of the process if challenged. A proper audit trail could be as simple as the custodian supplying a screenshot (ALT-Print Screen) of the details panel for the latest backup (as seen when one hovers over backups in Devices Preferences, as described above and seen in Fig. below).  A second approach is the use of cryptographic hashing, and a third, the use of remote screen-sharing and -recording software to permit step-by-step oversight of the work by the sponsoring witness or designee. Also, device backup sets may be sampled and tested for accuracy and completeness. It’s important to do something to audit and verify the effort; but proportionality suggests you needn’t do everything.
A second approach is the use of cryptographic hashing, and a third, the use of remote screen-sharing and -recording software to permit step-by-step oversight of the work by the sponsoring witness or designee. Also, device backup sets may be sampled and tested for accuracy and completeness. It’s important to do something to audit and verify the effort; but proportionality suggests you needn’t do everything.
What You Won’t Get with a Backup
An iPhone backup won’t preserve e-mail stored on the iPhone. This is by design. Per Apple, an unencrypted iTunes backup also won’t include:
- Content from the iTunes and App Stores, or PDFs downloaded directly to iBooks
- Content synced from iTunes, like imported MP3s or CDs, videos, books, and photos
- Photos already stored in the cloud, like My Photo Stream, and iCloud Photo Library
- Touch ID settings
- Apple Pay information and settings
- Activity, Health and Keychain data
Why not use iCloud?
At some point, you will use iCloud for preservation; but currently, an iCloud backup is not equal to an iTunes backup. It preserves less data, and byte-for-byte, it takes more time to create than an iTunes backup. Additionally, iCloud encrypts all backups, making them a future challenge for processing and search should a user’s credentials be unavailable.
Why an Unencrypted Backup?
This is a compromise. On the one hand, an encrypted iTunes backup preserves more information than an unencrypted backup. Apple won’t store passwords, website history, Health data and Wi-Fi settings in an unencrypted backup. On the other hand, many tools can’t process the contents of an encrypted backup, even with user credentials, and no tool can process an encrypted backup without credentials. Accordingly, we collect the data as an unencrypted backup, obviating the need for user credentials. To protect the data and add efficiency, we compress and optionally encrypt the backup set using credentials chosen for the legal hold project, not each user’s credentials.
Encryption
Encryption is a crucial security tool to protect client data collected in e-discovery, but it’s better to manage credentials systematically for the e-discovery project instead of according to each custodian’s preference. However, because mobile devices employ layers of encryption, obtaining an unencrypted backup won’t serve to unlock encrypted application data. You must obtain and preserve the user’s access credentials for that data.
Many users employ the same password for multiple sources, so requiring a user to disclose credentials serves to compromise the security of sources not collected. Assuage concerns by detailing steps taken to protect users’ credentials. An unlocked spreadsheet with each custodian’s password(s) may be a convenience for the legal team, but it’s a cybersecurity nightmare. Keep that in mind when furnishing credentials to service providers, and be sure your vendors are handling passwords securely.
Why Compress the Backup Data?
One reason we compress the data to a Zip file is to make it easier to copy to new media. Smaller data volumes move faster. However, depending upon the composition of the data backed up, the compressed Zip file may be much smaller or hardly smaller at all. My backup set compressed by just 2%. Much of the data on my iPhone consists of JPEG photos already in a compressed format, and it’s hard to compress data that’s already compressed as there’s little ‘space’ to squeeze out by further compression.
So why bother compressing the backup files?
Two reasons. First, placing the preserved data in a Zip file guards against overwriting the data by a subsequent backup of the device. Second, depending upon the Zip tool employed to compress the file, the Zip process affords a means to securely encrypt the data without having to install an encryption tool. Every Windows machine can create compressed and encrypted Zip files, so will every Mac running OS X.
A New Paradigm in Mobile Device Preservation
Recently, I wrote a post where I stated, “Today, if you fail to advise clients to preserve relevant and unique mobile data when under a preservation duty, you’re committing malpractice.” I’ll go further and add that competent counsel not only tells clients what they must do but must also help clients identify practical, proportional ways to meet mobile preservation obligations. This article lays out one scalable, defensible and cost-effective way to preserve iPhone and iPad content. The purpose is to debunk claims that mobile preservation is unduly burdensome, expensive and disruptive. Practical approaches are out there for other phones and devices, too. It’s our duty to insure our clients know about them and use them.
Acknowledgments: My thanks to Scott Moulton of Woodstock, GA, and a tip of the hat to Jacob Small of J. Madison PLC of McLean, VA, who shared his approach to custodial preservation of iPhones. Jacob’s method calls for creating a video record of the screen throughout the acquisition process. Some may want to do that, although I regard it as overkill in consideration of a custodian’s limited ability to manipulate the backup process and the potential to compromise other data if the custodian accesses sensitive information while waiting for the backup to complete. Jacob also directs custodians to open a terminal interface for command line access to complete a SHA-1 hash. I’m not comfortable steering custodians to the command line. There are easier, safer ways to generate a hash value.
******************************************************************************
APPENDIX: Exemplar iPhone Backup Instruction for Custodian-Directed Backup
[NOTE: This draft directive is offered to assist counsel in formulating language suited to the needs of the case and controlling law. It is not a form to be deployed without counsel. This example omits optional steps to encrypt the data set and transfer same to a distal repository for preservation, as such steps are frequently unnecessary to meet preservation duties].
Dear [Custodian]:
You recently acknowledged your obligation to preserve information relevant to a dispute between our company and ______________. Please see the _____________ hold notice for further details.
Within 48 hours of your receipt of this notice, you must preserve the contents of your company-issued iPhone. If you cannot comply, please advise me at once by e-mail or phone. Time is of the essence.
You must make an unencrypted backup using iTunes and compress the backup folder per the instructions below. Do not assume that you have been automatically making an unencrypted backup or preserving what’s required using iCloud. You must carefully follow the procedures set out below.
What you will need:
- Your company-issued iPhone and its USB charge/sync cable;
- Your company-issued desktop or laptop computer with the iTunes program installed. The computer must have available (unused) storage space on its boot (C:) drive exceeding twice the storage capacity of the iPhone. That is, if you have a 128GB capacity iPhone, use a computer with at least 256GB of unused storage space on its C: drive. You can find the capacity of the iPhone in Settings>General>About>Capacity. You can find the available storage on your computer’s boot (C:) drive using File Explorer on a Windows machine or Finder on a Mac.
Time Required: One to two hours (most of it unattended “machine” time)
It will take about 10-15 minutes to follow these instructions, update iTunes, if needed, and begin the backup. The backup will complete in under 30 minutes, and you can continue to use the phone during the backup process (but don’t disconnect the charge/sync cable). Then, it should take less than an hour to compress the data and 10 minutes or so to confirm successful compression and report on results. So long as the computer is secure and powered up throughout the process, you do not need to supervise, or leave the iPhone connected once backup completes.
Follow These Steps:
- Open iTunes and check for updates (Help>Check for Updates). Install the latest version of iTunes if not installed.
- Connect your iPhone to a USB 2.0 or 3.0 port on the computer using a USB charge/sync cable.
- If a message asks for your device passcode or to Trust This Computer, follow the onscreen steps.
 Select your iPhone when it appears in iTunes.
Select your iPhone when it appears in iTunes.
Click Summary in the sidebar.- In the Summary pane, be sure to uncheck “Encrypt iPhone Backup,” then click “Back Up Now.” You need not otherwise modify your Backups settings.
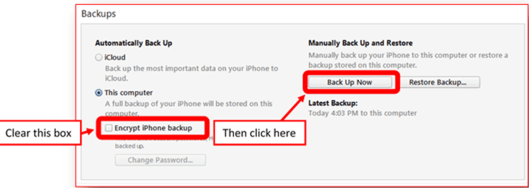
- Monitor the progress of the backup at the top center of the iTunes window. After the process ends, see if your backup finished successfully. If you’re using iTunes for Windows, choose Edit>Preferences>Devices from the menu bar at the top of the iTunes window. If you’re using iTunes for Mac, go to iTunes Preferences>Devices. You should see the name of your device with the date and time that iTunes created the backup. If you see beside the name of your device, you need to be certain you unchecked “Encrypt iPhone Backup” and repeat the process until you do not see beside the name of your device.
- You can now disconnect your phone from the computer.
- Locate the backup folder:
- Windows: Using File Explore, navigate to
C:\Users\your account name\AppData\Roaming\AppleComputer\MobileSync\Backup\ where “your account name” is the name of your Window’s User ID on the machine.
Mac: Using Finder, select Go>Go to Folder on the Finder menu and enter: ~/Library/Application Support/MobileSync/Backup/
In both Windows and Mac, the Backup folder will contain one or more subfolders with 40-character names like 12da34bf5678900386c48267658d340eb34007f8. If there are multiple subfolders, identify the subfolder that has the last modified date and time that matches the time you started this backup.
 9. Compress the contents of the subfolder: In Windows, right click on the subfolder just identified and select “Send to>Compressed (zipped) folder.” A progress panel like the one at right should appear. On a Mac, right click on the subfolder and select “Compress.” Do not turn off your computer or reboot. Allow the compression process to complete. It could take less than an hour to finish depending upon the type and volume of data backed up.
9. Compress the contents of the subfolder: In Windows, right click on the subfolder just identified and select “Send to>Compressed (zipped) folder.” A progress panel like the one at right should appear. On a Mac, right click on the subfolder and select “Compress.” Do not turn off your computer or reboot. Allow the compression process to complete. It could take less than an hour to finish depending upon the type and volume of data backed up.
10. Once compression has completed, Windows users should again navigate to the backup folder (see step 8 above) to confirm the presence of a file with the same name as the subfolder you identified but with the file extension .zip. Record the name, date/time and size of the zip file. [If you cannot see file extensions on your Windows machine, open “My Computer,” click “Tools” and click “Folder Options” or click “View” and then “Options” depending on your version of Windows. In the Folder Options window, click the “View” tab. Uncheck the box that says, “Hide file extensions for known file types.” This should make file extensions visible.]
11. By reply e-mail, send the name, date/time and size of the zip file you just created. Do not delete or open this file. It must be preserved without alteration until further notice.
Your supervisor is copied here to insure you are afforded the time, oversight and support needed to comply in a timely way. Thank you for your cooperation. Call me at ____________ with any questions.

Kimberly Christie said:
Great article! So how do I view and search the compressed zip file under the user’s iTunes account?
LikeLike
craigball said:
I’m confused by the question. You wouldn’t use an iTunes account to view or search a .Zip file. Here, the .Zip format merely serves to encapsulate the data to, inter alia, prevent it from being overwritten by a subsequent backup and facilitate encryption to protect the data in transit. You would UNzip the data for processing and use any of a number of processing tools to unpack the data, if it must be searched and reviewed in discovery. This post soley concerns preservation. I will address processing and review options in a future post. It’s not a topic that should be addressed in a cursory fashion as the data required to be reviewed and the preferred workflows vary from firm to firm and case to case. I’d first want to know what the firm currently uses to conduct review of ESI in e-discovery and seek to match the deliverables to the preferred review platform.
LikeLike
Kyle said:
Can you suggest any tools that can process the backup or is that typically the domain of a vendor? Is it common to turn over the whole of the backup or just piecemeal based on the relevant texts or app data?
LikeLike
craigball said:
Vendors can do it, but there are plenty of apps available depending upon the needs of the case and the preferred review platform. I hate to fall back on, “it depends,” but it does. By way of example, there’s a nifty app called FonePaw that does a good job parsing the backup and exporting selected contents to reports and delimited file formats.
Selecting the right processing tools requires consideration of what you need to process, the scale at which you must process the data and the structure of the deliverable. You also want to consider auditability as a factor in the defensibility of the selection. How can you show the tool “worked” (however you define success)?
It is NOT common to turn over the whole backup to an opponent. I think it would be grossly negligent to do so in most situations. It’s akin to letting an opponent root around in the client’s home, except more dangerous to the client’s interests. So, yes, piecemeal based on relevance and privileged character.
LikeLike
Mike McBride said:
Excellent look at using a backup as a preservation practice, but here’s the obvious question about mobile device backups that I wonder if you have a response to. What if the device isn’t owned by the org? In the BYOD world where employees are using their personal devices to communicate with business contacts, can you really expect a custodian to backup all of their texts and other personal information and hand it over to their employer? Personally, I wouldn’t do it.
LikeLike
craigball said:
Dear Mike: Here, we were dealing with company-owener phones and computers. But YES, I really DO expect a custodian to *backup* their personal device when the custodian is subject to litigation hold and the employee-owned device holds relevant data. But, let’s not conflate that duty with an obligation to “hand it over to their employer.” Very different duties and each requires different safeguards. Still, the data must be preserved before we can figure out who gets what, and the protocol I put forward makes it simple for that to be done and for the custodian to hang onto their sensitive data in a manner that effectively preserves its integrity and privacy. If the time comes for relevant data to be processed out of the backup and some of that data to be furnished to the employer, then provisions must be made to meet that goal without compromising legitimate privacy interests. Nowhere do I propose that private data be surrendered willy-nilly. The principle I stated at the start was: “Legitimate concerns respecting personal privacy and privilege do not justify a failure to preserve relevant mobile data, although they will dictate how data is protected, processed, searched, reviewed and produced.”
All the custodian surrenders here is the name and size of the backup set. Nothing else. I cant see how that would bother anyone unless they wear a tinfoil helmet. There are other posts coming that will make it clear that it’s feasible to separate baby and bath water, protecting everyone’s interests. It’s not fundamentally different than dealing with business data on a home computer. It requires some special handling, but no one kicked down doors. Patience, my friend, patience. 😉
LikeLike
Mike McBride said:
Fair enough, I await your further discussion, but the home computer is a good analogy, and one where I’ve run into too many people who want to forensically image all the home computers, or mobile devices, of their employees, which always gives me pause. I’m not necessarily a tinfoil hat wearer, but I am a huge proponent of clients and law firms not storing, and trying to safeguard, data they shouldn’t have in the first place. 😉
LikeLike
craigball said:
Opression aside, employers may compel employees to surrender relevant, non-privileged material stored in the employee’s personal devices. Location little matters. But, entitlement to a cookie doesn’t give employers the right to take the whole jar. There’s a balance to be struck, and employers better start thinking about same. We need to be a bit more European in this country when it comes to e-disocvery and sex –although not necessarily in that order.
LikeLike
Jesse Wilkins said:
As far as I know, in order to search said ESI you’d have to restore that backup and search through it – and I believe it has to be done on the physical device in question. There may be tools out there of which I’m unaware, and I’m sure there probably will be soon if there aren’t yet. But this is essentially no different IMO than recommending that companies look to backups as a primary mechanism for preserving information from individuals’ computers, systems, etc. I’d love to hear thoughts as to why this wouldn’t be the case, or if it is, why this wouldn’t be subject to the same sorts of issues around accessibility & cost shifting as other cases involving (primarily) email backups. The volume in question could still be hundreds of GB per device, and you’re still looking at each device = its own backup and its own inaccessible without restoration silo.
LikeLike
craigball said:
No, sir. Not at all. The data in the zip file need not be restored to a phone to be processed and searched. Not sure where you get that idea. Care to expand please?
Increasingly, e-discovery tools can work with the data natively as it’s not complex for any tool that groks SQLite data. There are also quite a few low cost apps that one can obtain online that do a good job unpacking the backup set and parsing it out as messages, call records, photos, video, etc., etc.
It’s inapt to liken this data to Exchange server backups on tape. The challenge of tape was its slow, linear interface, complex organization and bespoke compression scheme. None of that applies to an unencrypted iPhone backup. It’s native data. It’s more akin to a custodian’s PC, except unlike a forensic image of a computer, the backup doesn’t collect the complete OS and unallocated clusters. So, it’s much smaller and quick to acquire.
The only thing backup tapes and an iPhone backup have in common is the word “backup;”. Else, they are night and day. Try the method and see for yourself. Then, if you want to see how easy it is to access the content in the backup, use the free trial version of one of the many apps that make short work of the data. I mentioned FonePaw in an earlier reply, but there are lots out there.
Not. Rocket. Science. I promise.
Okay, if you don’t like my approach and clearly have strong views on same, what’s your superior solution? Thanks for weighing in.
LikeLike
Pingback: Custodian-Directed Preservation of iPhone Data can be Simple, Scalable and Proportional – NightOwl Discovery
Pingback: Preserving Mobile Data in Anticipation of Litigation | Oregon Law Practice Management
Puneet Tiwari said:
Hi Craig,
Great article. However there is a better solution. Check out *******, a tool for lawyers that allows for custodian self-preservation.
LikeLike
craigball said:
C’mon, a “better” solution that 1)is not free, 2)is in beta 3)is not produced by a company that is a household name like Apple and 4)stores sensitive, commingled data in a foreign country on servers with no accountability to U.S. authorities or under the jurisdiction of U.S. courts? Does better mean something different in Canadian parlance, like “Pierre slammed me in the face with his hockey stick, and now my face looks better all swollen and bleeding?”
LikeLike
WTKJD said:
I’ve been doing this for at least five years and used iBackup Extractor to pull the backups. It was also a first step when collecting laptops where the user also had a smartphone. There are similar backup tools for Android as well. Ran into some difficulty when the users were not issued a PC or laptop by the company or the company did not want to install iTunes in their standard image. But otherwise a solid way to capture a lot of data. We also would use iTunes to encrypt the backup with temporary credentials of our choosing and then had the user revert to their personal credentials. A solid eDisco hack!
LikeLike
craigball said:
If the post gets the Bill Kellerman Stamp of Approval, I’m beaming!
LikeLike
Lora Ramsey said:
This is a helpful post. Thanks for writing it. When I tried walking through the steps myself, I found that I was unable to uncheck the “Encrypt iPhone backup” as it is greyed out. Any ideas?
LikeLike
craigball said:
May I ask what versions of iPhone, iOS software amd iTunes you are using please? If it would not compromise any of your private information, a screenshot would help.
LikeLike
Lora Ramsey said:
It turns out I have encountered this problem because I previously backed my phone up to this computer and encrypted the backup. There are a couple of ways to get an unencrypted backup even if you have previously encrypted the backup on that computer. It seems the easiest way to deal with this is to use a computer you have not previously used to create a backup of your phone. Another option is to back the phone up to the icloud, wipe the phone, restore it from the icloud backup, and then back it up to iTunes.
LikeLike
craigball said:
That seems a lot of trouble. Perhaps simply deleting the old encrypted backup and re-starting iTunes might make a difference?
LikeLike
craigball said:
The options you outline are reported to work IF you first disable find my iPhone with your iCloud passphrase. I gather the point of making it difficult to re-initiate UNencrypted backups is to deny an easy path to prying eyes with physical access to the device from getting to the data of someone who has evinced a desire to prevent same by turning encrypted backups on. It definietly can be undone, based on my research of Apple support articles.
LikeLike
Lora Ramsey said:
i have a further update: neither of the options above worked.
LikeLike
Lora Ramsey said:
Simply deleting the backup and trying again will not work.
LikeLike
Jeff said:
Greetings all. Great article Craig. I was looking for precisely this type of information. Additionally, I was looking for an opinion on the defensibility of Time Capsule backup of a Mac. If it is defensible, you could preserve with very little cost.
LikeLike
craigball said:
The defensibility of a Time Capsule backup will naturally hinge on the nature of the risk. Viz, how will the integrity of the preservation be attacked? What is the ability of the custodian to game the data? My gut sense is it’s easier for custodians to alter a Time Capsule backup than an iPhone backup, but I haven’t done any work to test that expectation.
LikeLike
Pingback: Mobile to the Mainstream | Ball in your Court
Pingback: How Will We Back Up iPhones Without iTunes? | Ball in your Court
Pingback: Preserving Android Evidence: Return of the Clones? | Ball in your Court
Pingback: Atkinson-Baker | Preserving Android Evidence