 Social Media Content (SMC) is a rich source of evidence. Photos and posts shed light on claims of disability and damages, establish malicious intent and support challenges to parental fitness–to say nothing of criminals who post selfies at crime scenes or holding stolen goods, drugs and weapons. SMC may expose propensity to violence, hate speech, racial animus, misogyny or mental instability (even at the highest levels of government). SMC is increasingly a medium for business messaging and the primary channel for cross-border communications. In short, SMC and messaging are heirs-apparent to e-mail in their importance to e-discovery.
Social Media Content (SMC) is a rich source of evidence. Photos and posts shed light on claims of disability and damages, establish malicious intent and support challenges to parental fitness–to say nothing of criminals who post selfies at crime scenes or holding stolen goods, drugs and weapons. SMC may expose propensity to violence, hate speech, racial animus, misogyny or mental instability (even at the highest levels of government). SMC is increasingly a medium for business messaging and the primary channel for cross-border communications. In short, SMC and messaging are heirs-apparent to e-mail in their importance to e-discovery.
Competence demands swift identification and preservation of SMC.
Screen shots of SMC are notoriously unreliable, tedious to collect and inherently unsearchable. Applications like X1 Social Discovery and service providers like Hanzo can help with SMC preservation; but frequently the task demands little technical savvy and no specialized tools. Major SMC sites offer straightforward ways users can access and download their content. Armed with a client’s login credentials, lawyers, too, can undertake the ministerial task of preserving SMC without greater risk of becoming a witness than if they’d photocopied paper records.
Collecting your Client’s SMC
Collecting SMC is a two-step process of requesting the data followed by downloading. Minutes to hours or longer may elapse between a request and download availability. Having your client handle collection weakens the chain of custody; so, instruct the client to forward download links to you or your designee for collection. Better yet, do it all yourself.
Obtain your client’s user ID and password for each account and written consent to collect. Instruct your client to change account passwords for your use, re-enabling customary passwords following collection. Clients may need to temporarily disable two-factor account security. Download data promptly as downloads are available briefly.
Collection Steps for Seven Social Media Sites
Facebook: After login, go to Settings>Your Facebook Information>Download Your Information. Select the data and date ranges to collect (e.g., Posts, Messages, Photos, Comments, Friends, etc.). Facebook will e-mail the account holder when the data is ready for download (from the Available Copies tab on the user’s Download Your Information page). Facebook also offers an Access Your Information link for review before download. Continue reading



 I just got my Apple Card and, while I hardly need another credit card, I thought readers might be curious what the fuss is about. After all, it’s just a credit card, right?
I just got my Apple Card and, while I hardly need another credit card, I thought readers might be curious what the fuss is about. After all, it’s just a credit card, right? Although my Apple Pay credit account went live in a minute, as with all physical credit cards, the Apple Card must be activated before use. For most cards, this requires time online or a phone call where you dial or speak a lot of digits. With the Apple Card, you just hold
Although my Apple Pay credit account went live in a minute, as with all physical credit cards, the Apple Card must be activated before use. For most cards, this requires time online or a phone call where you dial or speak a lot of digits. With the Apple Card, you just hold 

 If you want to know the card number and CID for the Apple Card, you must retrieve them in Wallet. That’s a genuine layer of security. By the same token, heaven help anyone who comes across a neanderthal with a carbon charge slip (anyone remember those?) who tries to rub transfer the card number.
If you want to know the card number and CID for the Apple Card, you must retrieve them in Wallet. That’s a genuine layer of security. By the same token, heaven help anyone who comes across a neanderthal with a carbon charge slip (anyone remember those?) who tries to rub transfer the card number.





 Two-and-a-half years ago, I concluded a
Two-and-a-half years ago, I concluded a  It’s the month for giving thanks, and I’m ever-grateful for the daily e-discovery blog penned by my friend, Doug Austin, for CloudNine. It’s tough to get out a post every business day, and Doug’s done it splendidly for, what, nine years now? Kudos! Doug’s
It’s the month for giving thanks, and I’m ever-grateful for the daily e-discovery blog penned by my friend, Doug Austin, for CloudNine. It’s tough to get out a post every business day, and Doug’s done it splendidly for, what, nine years now? Kudos! Doug’s 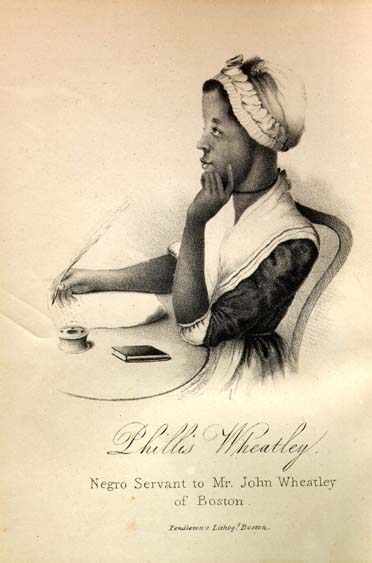 In 1829, Georgia made it a crime to teach slaves to read. Literate slaves threatened the control of their masters. If a slave could read the Bible, a slave could also circulate an inflammatory pamphlet or forge a pass. Literacy was a step to freedom. So, with Georgia on my mind, I ask, Are e-literate requesting parties a threat to th status quo?
In 1829, Georgia made it a crime to teach slaves to read. Literate slaves threatened the control of their masters. If a slave could read the Bible, a slave could also circulate an inflammatory pamphlet or forge a pass. Literacy was a step to freedom. So, with Georgia on my mind, I ask, Are e-literate requesting parties a threat to th status quo?